Table of Contents
What is klouddb_shield ?
Klouddb_Shield is an open source security tool that checks for CIS compliance( https://www.cisecurity.org/cis-benchmarks/) . Currently we check for about 32 controls(Postgres) and we plan to add more checks soon
We tested this tool on CentOS and Ubuntu ( PG 14 and PG13), It also includes 46 MySQL controls so a total of 78 checks as of today .. More checks will be added soon
How to run this tool on my server ?
You can directly download the package from releases section of repo https://github.com/klouddb/klouddbshield and install the package (for example – rpm for centos ; deb package for Ubuntu etc..)
Once you install it , you need to populate the config file under /etc/klouddbshield folder . Please fill username , dbname and password (Check github readme for a sample format)
Once the config file is populated please run ‘ciscollector -r’, it prompts you to enter 1 or 2 and kindly enter 1 for Postgres(Example run given below)
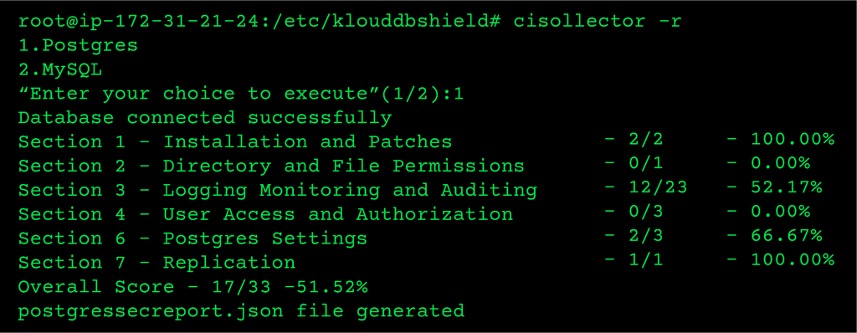
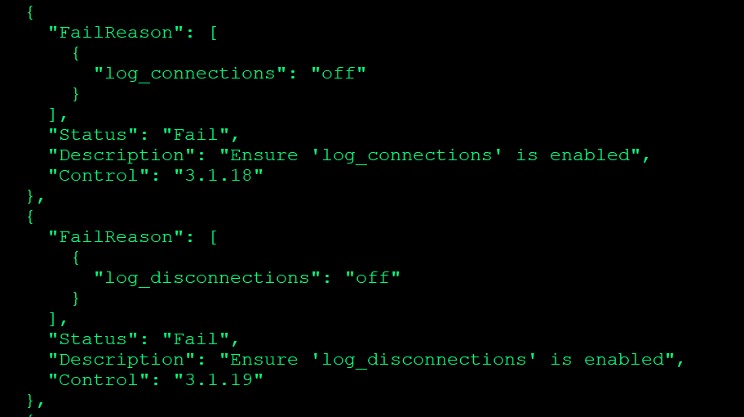
How to read the json output file generated ?
For each control you will get a PASS or FAIL as status . If it is FAIL you also can see the reason for failure . For example in below snapshot you can see that log_connections is turned off and that is a FAIL
Section 1 and 2 - Operating system and file permissions
1.2 checks if systemd service files are enabled for postgres
Enabling the systemd service on the OS ensures the database service is active when a change of state occurs as in the case of a system startup or reboot.
1.3 Runs check_db_dir to validate if postgres is initialized properly or not
PostgreSQL enforces ownership and permissions of the data cluster such that:
- An initialized data cluster is owned by the UNIX account that created it.
- The data cluster cannot be accessed by other UNIX user accounts.
- The data-cluster cannot be created or owned by root
- The PostgreSQL process cannot be invoked by root nor any UNIX user account other than the owner of the data cluster.
Incorrectly instantiating the data cluster will result in a failed installation.
2.1 Ensure the file permissions mask is correct
This control checks if the umask for postgres user is restrictive or not (077 or more)
Section 3 - Logging settings
This section audits logging configurations .. Below are some of the checks but it does a total of 23 checks (for section 3) – Not all are included in below table
| # | Checks | ||||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1 | Ensure the logging collector is enabled | ||||||||||||
| 2 | Ensure the log destinations are set correctly | ||||||||||||
| 3 | Ensure the log file destination directory is set correctly | ||||||||||||
| 4 | Ensure the filename pattern for log files is set correctly | ||||||||||||
| 5 | Ensure log_connections is turned on | ||||||||||||
| 6 | Ensure log_disconnections is turned on | ||||||||||||
| 7 | Ensure proper log truncation and retention methods are chosen | ||||||||||||
| 8 | Ensure proper values are chosen for debug_print_parse , debug_print_plan , etc.. | ||||||||||||
We also check if pgaudit extension is enabled or not (pgaudit extension can help in auditing db activity)
Section 6 - SSL , FIPS openssl cryptography and other checks
In this section we make sure that SSL is enabled , We also check if FIPS 140-2 OpenSSL Cryptography Is Used
Federal Information Processing Standard (FIPS) Publication 140-2 is a computer security standard developed by a U.S. Government and industry working group for validating the quality of cryptographic modules. Use of weak, or untested, encryption algorithms undermines the purposes of utilizing encryption to protect data. PostgreSQL uses OpenSSL for the underlying encryption layer.
Section 7 - Archive_mode check
In this section we check if archive_mode is enabled or not . We also check if archive_command has a proper value
Skipped controls
In this release we are including 32 controls . We skipped some controls as they can not be automated . We will include more controls in future releases
References
Control documentation reference used is given below
https://www.cisecurity.org/cis-benchmarks/
Summary
We released KloudDB Shield 1.1(first version that includes postgres checks) today . Please give it a try and pass your feedback . We spent ton of time to develop this tool and we plan to enhance this tool based on user feedback
Also check our performance articles –Pg_fincore and pg_buffercache to troubleshoot performance issues , Pgbouncer multiple instances(How we increased our TPS using multiple instances) , Postgres and temporary files , Pgpool and performance tuning, How we improved Lambda performance by 130x etc..
Looking for Postgres support ? Please reach us at support@klouddb.io
